Blog ISO 27001
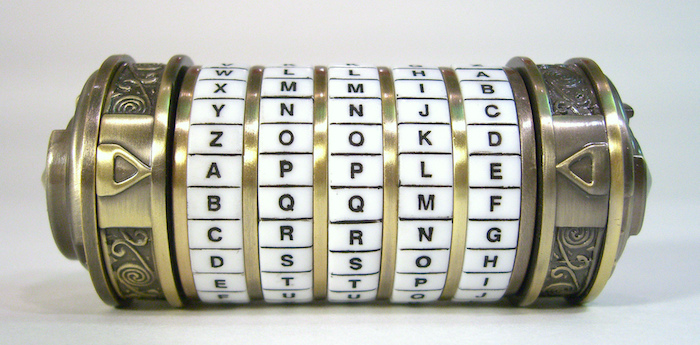
Information security – Cryptographic controls policy example
Using cryptographic controls such as encryption can help with information security, but only if it is applied correctly. To make sure it is used in the right way, it is recommended by standards such as ISO 27002 have a data encryption policy. In this article we share the ICT Institute data encryption policy, that is…
Sieuwert van Otterloo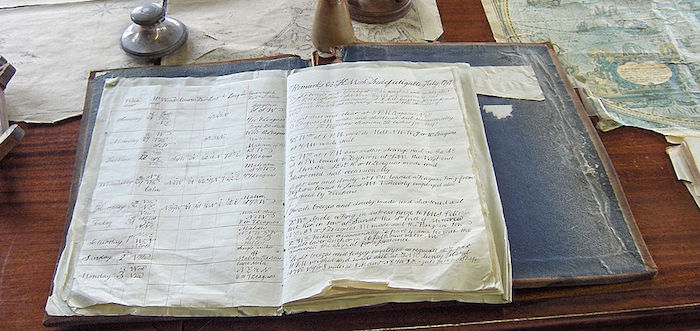
Information security – asset inventory
One of the first steps in setting up an information security management system is to create an inventory of information assets. It is in important step to make sure the right measures will be taken: the assets are the basis for identifying risks, and thus for the measures that will be taken to mitigate risks.
Sieuwert van Otterloo
A basic risk management method for information security
One of the requirements for good information security is to have a method for risk identification and assessment. This article describes one simple and practical method that can be used by any organisation.
Sieuwert van Otterloo
