Enabling two-factor authentication: highly recommended
| Joost Schalken-Pinkster |
Security

Many websites, including giants such as google, Facebook and Dropbox, have implemented an additional security feature called two-factor authentication. Unfortunately this extra security feature is normally turned off. We recommend turning two-factor authentication on immediately, because it will protect your account from being hacked.
What is two-factor authentication
Most websites ask for a username and password when you try to log-in. Security experts call this one-factor authentication: exactly one piece of information, the password, is used to authenticate that you are who you say you are. One-factor authentication provides some level of security but is often broken, either because passwords are stolen from the website or when the user leaks the password. In a previous post we already gave recommendations on choosing passwords and this helps a little bit. To increase security further, you need more than just a password. This is exactly what two-factor authorisation is: using additional security measures on top of just a password.
Two factor authentication examples
There are many different methods for two-factor authentication, each with its own variants. We use the term loosely to mean anything better than password-only verification. Some other people also call it multifactor authentication or MFA. Two-factor authentication is often abbreviated as 2FA.
To give a bit of theory, there are three types of authentication factors, called credentials. We can base credentials on:
- on things we know (knowledge),
- on things we own (possession), or
- on who we are (physical properties of our body, also called biometrics).
These concepts do not just apply to websites, but also to physical security. If a building requires a key (possession) and has a fingerprint scanner (biometrics) it has two-factor authentication. If someone asks you to show your passport and checks the picture, this is also two-factor authentication based on possession and biometrics. A car usually only requires a key and thus only has one factor authentication. There is a tradeoff here in usability (cars can be easily shared) and security (cars are easily stolen when keys are lost). Also, biometrics work well for buildings and devices, but is difficult to execute remotely.
 Dutch banks also use two-factor authentication based on bank cards. Each customer has a small electronic device for authentication. The device reads the chip installed in each bank card and generate a number that proves to the bank IT system that you have your bank card. This system is a very secure way of implementing two factor authentication but is too expensive for most websites.
Dutch banks also use two-factor authentication based on bank cards. Each customer has a small electronic device for authentication. The device reads the chip installed in each bank card and generate a number that proves to the bank IT system that you have your bank card. This system is a very secure way of implementing two factor authentication but is too expensive for most websites.
Two-factor authentication on the web
There is a very useful website twofactorauth.org that maintains a list of websites that have offer two factor authentication. The following commonly used services have two-factor authentication. They typically have not made it mandatory so you need to turn it on. We have provided the links that describe how it works and how it can be turned on.
- Facebook https://www.facebook.com/help/148233965247823
- Gmail http://www.google.com/intl/en-US/landing/2step/features.html
- Twitter https://support.twitter.com/articles/20170388
- Dropbox https://www.dropbox.com/en/help/363
- Linkedin https://www.linkedin.com/help/linkedin/answer/531?lang=en
Example: Facebook
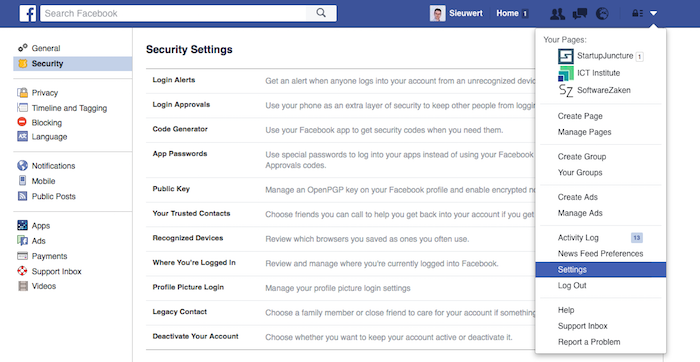
To use Facebook as an example: Facebook accounts are frequently hacked and this can lead to all kinds of damage, from embarrassment to identity theft. Facebook is often used as a login service for other websites and is also used professionally by people managing a company page. It is thus no surprise that Facebook offers additional security options. The screenshot below shows how you can use the top right menu to go to the settings. In settings you go to security and select Login approvals, the name Facebook uses for two factor authentication. If you turn this on you will get a text message with a confirmation code whenever you or someone else tries to login to your Facebook account.
Google and google authenticator
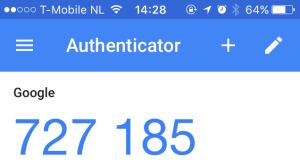 Google also takes security seriously and is offering a whole range of two factor authentication options. One of the most interesting options is the Google authenticator app. This app generates the confirmation codes based on a timer. The codes are valid for exactly one minute. After one minute, the app computes and shows the next code.
Google also takes security seriously and is offering a whole range of two factor authentication options. One of the most interesting options is the Google authenticator app. This app generates the confirmation codes based on a timer. The codes are valid for exactly one minute. After one minute, the app computes and shows the next code.
The main advantage of the authenticator app is that no text messages are needed. It thus also works when you are not in reach of the cellular network and it is slightly more efficient and cheaper for websites. The google authenticator is not just for google, it can also be used by other services. For instance Dropbox also offers the google authenticator as a two-factor authentication option.
Conclusion
Two-factor authentication is much more secure than password-only authentication. We therefore recommend anyone to turn on two factor authentication for all websites. Which variant is used does not really matter: both phone based and app based variants are much more secure than just a password. Please note that you must still choose your passwords carefully even when using two factor authentication. If you do this correctly , your accounts will be very difficult to hack.
Images: by the authors (Sieuwert van Otterloo and Joost Schalken) except for the keys images: creative commons by Brenda Starr.
Dr. Joost Schalken-Pinkster has obtained a Ph.D. in software engineering in 2007. Since then he has worked continuously in IT as architect management consultant and lecturer. Besides working at ICT Institute, Joost is lecturer at Utrecht Applied University where he focuses on code construction, software design and software architecture.