An overview of advanced persistent threats
| Sieuwert van Otterloo |
Security
Advanced Persistent Threats (APTs), are a new class of large, sophisticated and often international attacks. We have created an overview of publicly known APTs in order to determine whether APTs are indeed on the rise and what organisations should do to increase their resilience against APTs.
APT definition
The definition of an Advanced Persistent Threat is a cyber-attack with sophisticated tools, continued over a longer period of time. The term was coined in 2006 by the US Air Force to indicate attacks from hackers of one country against the infrastructure of another country. The first prime example of an APT was the StuxNet worm, discovered by the public in 2010. This piece of software, probably created by a western country, worked like a computer virus that would infect computers. Unlike previous viruses it would not spread at random and cause arbitrary damage. It only had an effect on one specific Uranium factory in Iran.
Security researchers have expanded the use of the term APT to included all kinds of large scale malware activities, diluting its original meaning. A better term, already used by some researchers is the ‘targeted attack’: a cyberattack not aimed at any Internet Users, but at a specific organisation, for instance for industrial espionage. For this article we have indeed used the definition of a sophisticated, targeted attack.
Number of APT per year
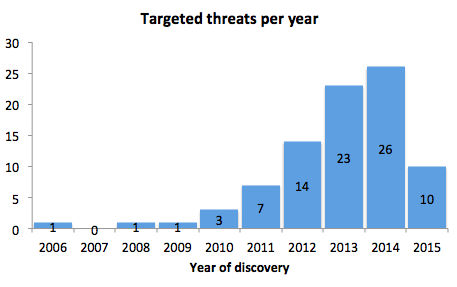 The following chart anshows the number of APTs described per year. This number is clearly on the rise: from one example in 2006 and zero in 2007, the number has increased to 26 in 2014. This number is based on analysis of data collected in APTnotes, an online repository of APT-related information. Using this data, a list of 86 unique threats was created.
The following chart anshows the number of APTs described per year. This number is clearly on the rise: from one example in 2006 and zero in 2007, the number has increased to 26 in 2014. This number is based on analysis of data collected in APTnotes, an online repository of APT-related information. Using this data, a list of 86 unique threats was created.
APT examples
The APTs on this list differ in size and importance. The following top ten consists of the most sophisticated, most widespread or otherwise interesting examples.
- Wicked Rose, the original APT in 2006 was targeting the US military and is suspected to be coordinated from China.
- Ghostnet, from 2009, is one of the oldest APTs. At the time of discovery it had infected 1295 hosts in 103 countries
- Stuxnet, the best known APT, surprised security researchers by using several previously unknown security issues. This indicates that the attackers are able to conduct their own security research.
- Operation Aurora discovered in 2010, took place in end of 2009. The goal was to steal or modify the source code of several US tech companies. The attack was first announced by Google, one of the victims
- Duqu, in 2010, was one of the most advanced attacks from 2010
- Uroburos / Turla / Snake, discovered in 2011, has the very sophisticated property that infected computers can communicate with each other, making it possible for attackers to manipulate computers even when they are not connected to the Internet
- Windigo, from 2015, uses multiple ways to attack computer. It has been able to take over several Unix and Linux servers, computers that are normally much less vulnerable. The reason is that Windigo is able to intercepts SSL sessions and capture credentials. The attackers use this data to log in to the computers.
Some smaller but interesting APTs in the list are the following:
- The Monju incident, reported in 2014, is about a single computer in a Japanese powerplant that had an infected media player. The incident could be a random event, or it could have been a first step in a nuclear attack. As the culprits have not been caught, we do not know for sure.
- The DarkHotel threat from 2014 was aimed solely at CEOs of organisations, and was able to infect these CEOs and follow them through the Wifi networks of hotel chains
- Anunak from 2014 was aimed specifically at banks. This was one of the most targeted attacks, aimed at only striking a few times but getting millions of dollars in each incident.
What do we know about APTs
One thing that has become clear in the analysis of APTs is that there is a wide range of targeted attacks out there. Many of the attacks that are called APTs are very sophisticated. They are based on original research of the creators, using unknown security holes (So-called zero day vulnerabilities).
Other attacks however are not sophisticated at all. Any student (not even IT-student) could mount an APT by collecting information from linkedin and twitter, writing some targeted fake emails and installing a publicly available remote administration tool. Several standard tools now exists, for instance Poison Ivy or njRAT.
Also worrying is that it is often not clear at all who is targeted by an APT and with what purpose. Most of the software in the wild just installs itself and waits for further orders. In many cases the researchers have not been able to find out what the ultimate goal of such an attack would be.
Recommendations
Targeted attacks are often targeted at many users at the same time, because they consists of multiple steps. Only when these multiple steps are completed is the attack successful. The best defence is therefor to make the organisation resilient by taking measures on all levels. For reference, we have included a typical layering model that we use when assessing security plans. As you see: IT is only half the solution in IT security, the other half should come from the whole organisations.
We recommend organisation to implement all of the following measures:
- Use Spam-filtering and instruct users not to open spam messages. Most attacks start by spam messages.
- Explain users that they should verify what websites they are surfing on. Many domains with unknown names are owned by malware-organisations
- Update and upgrade computers to newer, supported versions. Older software is often easier to exploit.
- Use anti-virus software. Half the attacks (the non-sophisticated ones) use previously discovered vulnerabilities and old tools.
- Use a firewall and monitor network traffic to stop malware from communicating. This will not stop all attacks as many APTs know how to circumvent this, but it makes life harder for attackers.
- Educate IT staff on IT security practices for infrastructure and coding, and make sure security is a priority in all IT activities and projects.
Dr. Sieuwert van Otterloo is a court-certified IT expert with interests in agile, security, software research and IT-contracts. He is a also an ISO 27001 and NEN 7510 auditor and AI researcher.

