Blog information security

ISO 27001 technological controls for software development
The latest version of ISO 27001 contains multiple controls about secure development, engineering, coding and testing that seem to overlap. In this article we provide guidance how to implement these controls. The overlapping controls explained are 8.25, 8.26, 8.27 and 8.28. We also cover 8.31 and 8.33 (test environments and test information).
Sieuwert van Otterloo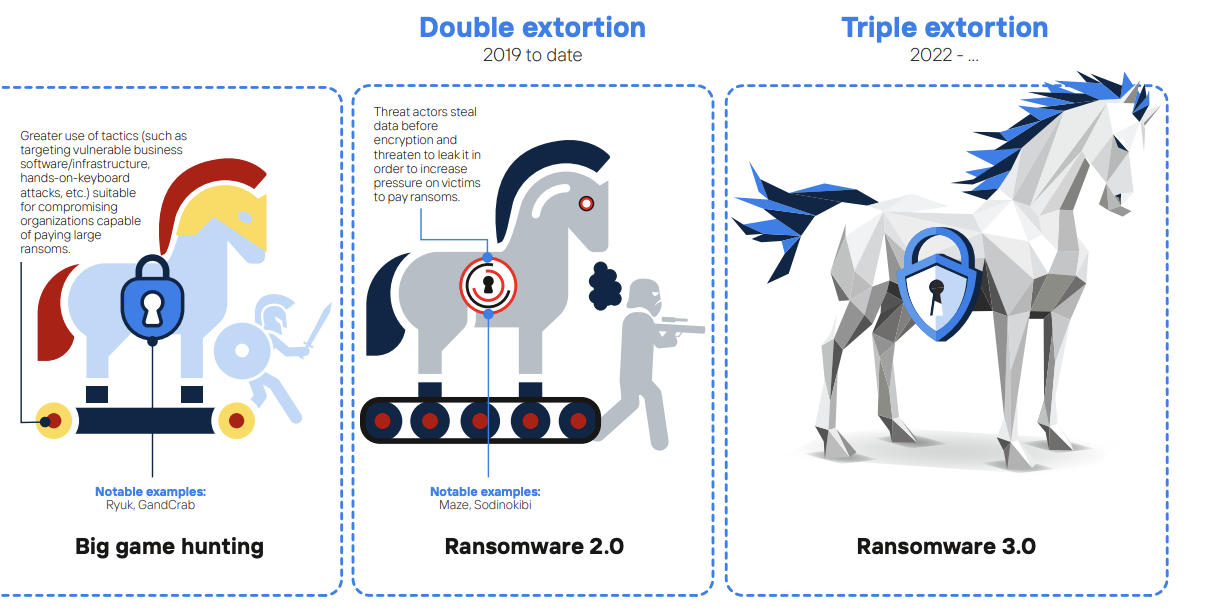
NOREA recommends CIS controls against ransomware
NOREA, the Dutch professional organisation of IT auditors, has conducted a study into a framework for ransomware measures, in response to the increasing ransomware attacks that have been reported in the news, both internationally and in the Netherlands. The use of ransomware has been around for quite some time, however it is very evident that…
Sieuwert van Otterloo
The NIS-2 Directive: raising the security bar in Europe
In the final days of December 2022, a new Information Security Directive has been published by the European Commission. The NIS-2 Directives, aimed at improving the resilience of Europe’s Network and Information Systems, succeeds and supersedes its older brother by both broadening the scope and taking into account the ever changing information security landscape. In…
Joost Krapels
Measuring and monitoring your ISO 27001 ISMS
Measuring and monitoring information security is required under clause 9.1 of ISO 27001. In this article we explain how to effectively monitor and measure your ISMS.
Joost Krapels
ISO27002:2022 explained – Technological controls
In this article, we explain the new ISO 27002:2022 chapter 8 – Technological controls. This covers the controls required to set up and maintain secure technological systems, particularly focusing on secure systems, development and code management. This is the last article in a series of four, each article covering one chapter: organization controls (chapter 5)…
Sieuwert van Otterloo
