Security+ explanation and practice questions
| Joost Krapels |
Security

Security+ is a certification offered by CompTIA. Those who have passed the exam, keep earning Continuous Education points, and pay the annual maintenance fee may add the title to their name. I (Joost) passed this exam recently and wanted to give you an impression of Security+, why you too might want to get certified, an overview of the certification process, and outline how you can prepare for the exam. At the end, we have included some example questions.
Security+ background
Security+ is a well-known entry level information security certification and has been around since March 2008. It touches upon most subdomains of information security, but does not go into great depth for any of them. Every few years, a new version is published. The previous version, SY0-501, launched in 2017 and retired in 2021. The current version, SY0-601, launched in 2020 and should be active for a few more years.
Security+ builds upon two other CompTIA certificates, Network+ and A+. Network+ focusses, as the name suggests, on computer and telecom networking. A+, on the other hand, aims to teach basic IT and IT support skills. The two exams are not a prerequisite for Security+.
The Security+ domains
The exam outline lists five domains to master. We’ve summed them up, and listed several of the subdomains they contain:
1. Threats, Attacks and Vulnerabilities (24%) Social engineering, password attacks, web application attacks, and network-related risks.
2. Architecture and Design (21%) Cloud computing, cloud security, secure software development, authentication, and resilience.
3. Implementation (25%) Secure protocols, network protection, wireless security, mobile devices, identity and access management.
4. Operations and Incidence Response (16%) Analysis and discovery tools, CLI commands, logging, and digital forensics.
5. Governance, Risk and Control (14%) Compliance, data loss preventions, legislation, privacy, and organizational controls.
Who’s it for?
CompTIA recommends roughly two years of experience working in information security before attempting the Security+ exam, and we agree with this. It is definitely not impossible with less than two years of experience, but if you decide to go this way, most concepts will be new to you. The two years of experience is a recommendation, not a requirement.
We recommend Security+ to anyone with no prior information security certifications and up to four years of experience in the field. It allows you to discover all the subdomains and which ones you would like to learn more about. With this level of experience, the exam is challenging but definitely doable. If you have four or more years of security experience, CISSP might be a better fit for you. CISSP is even broader than Security+, and goes into more depth on all topics. It does, however, require five years of relevant work experience and a lot more technical knowledge than Security+. After passing Security+, CISSP is a logical next target to strive for.
If auditing Information Security Management Systems is more your cup of tea, you might want to look into getting a CISA certification instead.
How to pass the exam
There is no study path that works for everyone, since everyone learns a different way. If you are relatively new to networking, it might be wise to follow an online course on that topic first, such as the Coursera Bits and Bytes of Computer Networking by Google, or Udemy Network+ course by Jason Dion. With (now) at least a general understanding of networking, we recommend following Jason Dion’s Udemy Security+ course. This is a great way to get acquainted with all the Security+ topics, and get a general feel for the depth of knowledge required. This course is, however, not a direct match with the CompTIA exam outline: it skips over quite a few details and also contains material not mentioned in the exam outline.
Another path to follow, or to follow simultaneously, is to go down the traditional book-route. The Security+ Study guide is very affordable, and contains all the knowledge you need. In addition to this, you get access to an online portal to practice all the book’s example questions in an interactive manner.
The exam consists of 80-90 questions, with non-native English speaking candidates being allotted 2.5 hours to complete them. Most questions are multiple-choice, but there are always three to five Performance-Based Questions (PQB’s). These PQB’s are drag and drop, match, or system configuration challenges. Some organizations offer special practice environments for the PQB’s, but most PQB’s can be passed if you understand the study material well enough and have some IT experience.
After the exam, you need to pay a maintenance fee of roughly €50 per year. If you wish to extend your certification for longer than the initial three years after your exam date, you must earn Continuous Education points and keep paying the maintenance fee.
Security+ practice questions
The following ten questions are a hint of what to expect on the real exam. We have created nine multiple choice questions, and one PBQ.
1. Your web server’s CPU, which normally hovers around 60% usage, jumped to 99% two minutes ago and is still at 99%. Which type of attack is MOST LIKELY happening?
a. SQL injection
b. Session replay
c. DHCP snooping
d. SYN-flood
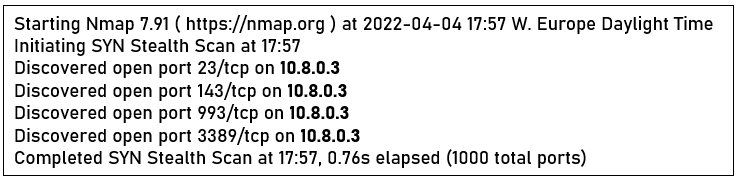
2. A recent Nmap scan showed that the following ports on your public-facing server are open. Which port should you worry about most?
a. 23
b. 143
c. 993
d. 3389
3. You have implemented a password history restriction of 10 passwords. Which other restriction should you put in place to prevent users from creating 11 new passwords so they can re-use their current password?
a. Maximum password age
b. Password complexity
c. Minimum password age
d. Password sharing
4. Greg has two hard drives, and wants to use the second one as a mirror. Which RAID level should he use?
a. RAID 0
b. RAID 1
c. RAID 5
d. RAID 6
5. What is the best way to make sure unauthorized individuals do not enter your organization’s HQ building?
a. Mantrap
b. CCTV system
c. IDS
d. Bollards
6. Which of the following systems is vulnerable to a Golden Ticket attack?
a. RADIUS
b. TACACS
c. TACACS+
d. Kerberos
7. Your organization plans to move their document storage to a Google Suite environment. What type of cloud solution is this?
a. Public cloud
b. Private cloud
c. Hybrid cloud
d. Offline cloud
8. You are the CISO at a school in Los Angeles, USA. Which of the following Laws and Regulations is most relevant for you?
a. SOX
b. GBLA
c. FERPA
d. GDPR
10. Put the following in order of least volatile to most volatile.
L3 CPU cache, Cloud back-up, Local logs, System memory, Routing table, Local back-up
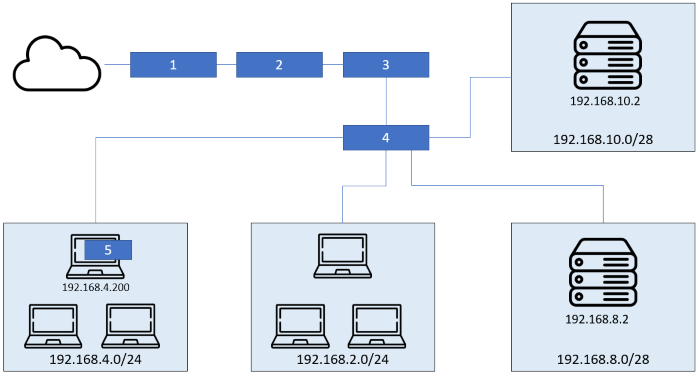
10. PBQ: Place the five protection mechanisms in their BEST place in this network diagram.
SWITCH, NIPS, FIREWALL, ROUTER, HIDS
Finished? Check your answers here
Image credit: @danny144 via Unsplash, icons via Flaticon
Joost Krapels has completed his BSc. Artificial Intelligence and MSc. Information Sciences at the VU Amsterdam. Within ICT Institute, Joost provides IT advice to clients, advises clients on Security and Privacy, and further develops our internal tools and templates.